Lazarus Group: hackers from country with no internet threaten defi

While not much is known about the Lazarus Group, researchers have attributed numerous cyber attacks to them over the past decade, as well as ties to Russia.
The most notorious crimes of Lazarus Group
The Lazarus Group (also known as the Guardians of Peace or the Whois Team) is a cybercriminal group with an unknown number of hackers.
One of the earliest attacks is known as “Operation Troy”, which took place from 2009–2012. In 2014, Lazarus attacked Sony Pictures Entertainment and stole over 276 thousand company files, immediately appearing on WikiLeaks. The stolen documents reveal the company’s immediate plans, the actors’ fees and working conditions, and most importantly, shed light on how Sony lobbies its interests in the government.
Kaspersky Lab reported in 2017 that Lazarus tended to focus on espionage and cyberattacks while a subgroup within their organization. Kaspersky called it Bluenoroff.
In February 2017, North Korean hackers stole $7 million from the South Korean exchange Bithumb. Youbit, another South Korean crypto platform, filed for bankruptcy in December 2017 after 17% of its assets were stolen in cyber attacks.
Since the beginning of 2021, Lazarus has also begun to carry out attacks on cybersecurity researchers and increased activity in decentralized finance.
One of the largest crypto hacks of all time occurred in 2022. Crypto gaming company Axie Infinity lost $620 million in cryptocurrency. Authorities later said North Korean cybercriminals linked to the Lazarus group were behind the massive theft.
Analysts also believe that Lazarus Group is responsible for hacks of other crypto companies, including Ronin sidechain, Atomic Wallet, Alphapo platform, and Horizon cross-chain bridge.
How many cryptocurrencies do Lazarus hackers have?
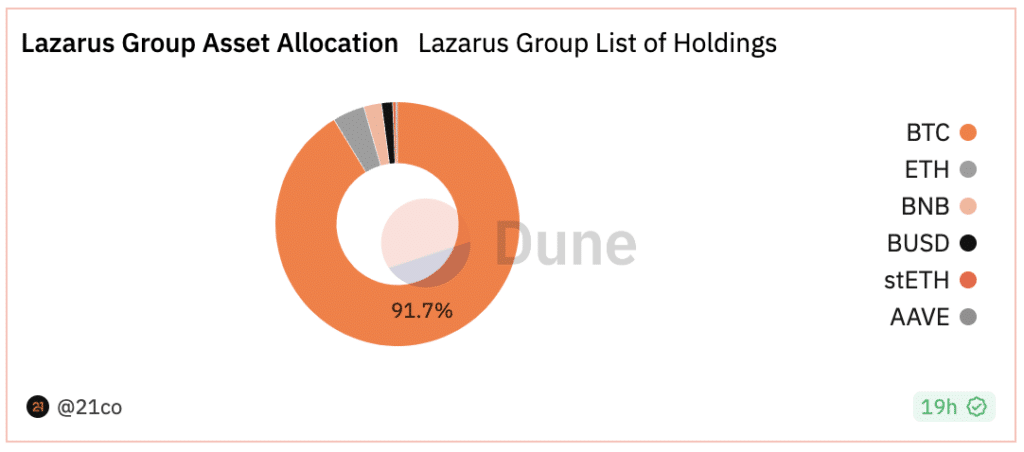
According to 21.co analysts, Lazarus Group owns cryptocurrency worth at least $45 million at the time of writing.
We are talking about 295 addresses that belong to the hacker group, according to information from the US Federal Bureau of Investigation and the Office of Foreign Assets Control.
Notably, cyber criminals do not store the so-called confidential coins: Monero, Dash, and Zcash, transactions with which are more difficult to track. Instead, 90% of their wealth comes from Bitcoin (BTC). The hackers’ portfolio also includes other popular cryptocurrencies – Ether (ETH), Binance Coin (BNB), Binance USD (BUSD), staked ether (stETH), and Aave (AAVE).
Connections with Russia
The first cases of targeted Lazarus attacks on Russia appeared at the beginning of 2019, but then there was a lull. Kaspersky Lab experts claim that Lazarus hackers often rob cryptocurrency traders using virus programs. Other Lazarus attacks in Russia are aimed at collecting data from organizations associated with research and production of goods, analysts said.
In 2023, Chananalysis experts said that hacker groups linked to North Korea were increasing their use of Russian crypto exchanges, which are known to launder illicit proceeds into crypto assets.
On-chain data showed that $21.9 million worth of cryptocurrency stolen from the Harmony protocol was transferred to a Russian exchange known for processing illegal transactions. Experts also claim that North Korean structures have been using Russian services, including this exchange, for money laundering since 2021.
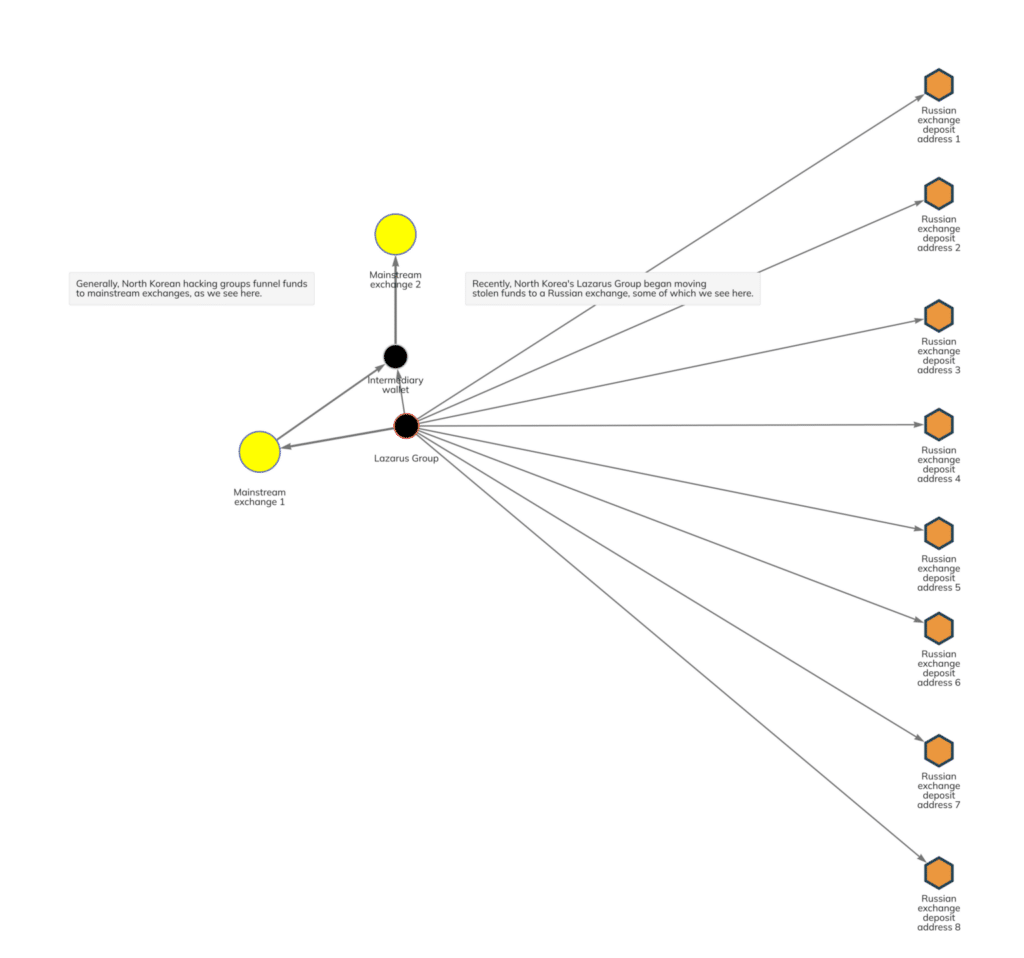
An alliance between North Korean and Russian cybercriminals poses a problem for global authorities. Russia is known to be unwilling to cooperate with international law enforcement efforts.
This makes the prospect of recovering stolen assets sent to Russian exchanges particularly bleak. While the major centralized exchanges that North Korean hackers have previously relied on tend to cooperate, Russian exchanges and law enforcement have a history of non-compliance, greatly reducing the likelihood of asset recovery.
Who is behind the North Korean hackers?
It is unclear who is behind the group, but many experts and media attribute Lazarus to close ties to the North Korean government.
Experts suggest that cybercrimes are committed to obtaining funds for the development of weapons, the purchase of fuel, and other resources. The anonymous nature of the cryptocurrency market allows transactions to be hidden, meaning that by paying for various goods with Bitcoins, North Korea can circumvent sanctions.
How country without internet supports hackers
Martin Williams, a fellow at the Stimson think tank, compares the process of training hackers in North Korea to the cultivation of Olympic champions in sports schools. Young people who have demonstrated the brightest abilities, ideological endurance, and sincere love for the authorities are allowed to continue their studies in higher educational institutions in the country. Some students end up receiving an offer from state security agencies that is difficult to refuse.
According to The New Yorker, the North Korean government has been unofficially supporting criminal groups since the 1970s that smuggled cigarettes, produced counterfeit dollar bills, and produced and distributed synthetic drugs in the region. Thus, encouraging online theft is not the birth of some fundamentally new phenomenon but an upgrade of an old one.