Computer Infected by Monero Malware? There’s a Workgroup for That

It seems like every day the crypto news zeitgeist is reporting on yet another Monero (XMR) malware hacking attempt. The scale is different from nations, individuals, and everyone in between, but the mechanism appears relatively the same. A simple Javascript Coinhive plug-in, a wallet, and one of the strongest privacy-centric cryptocurrencies on the Internet means just about anyone can be a victim as well as an attacker. Fortunately, the Monero community is actively combatting the dark side of pure privacy.
What Is Monero’s Workgroup?
On September 26, 2018, Monero contributor Justin Ehrenhofer announced the launch of the Monero Malware Response Workgroup. The premise? Inform, report, and protect users who may be looking to fight against XMR-financed malicious mining or merely rid their hardware of it.
The workgroup provides users who may have zero background knowledge on cryptocurrencies, let alone Monero. It includes educational resources that inform on what mining is and how best to stay protected. The entire operation is overseen by a group of volunteer-contributors from the Monero community who can be reached via Freenode, Slack, and Mattermost.
To get a better idea behind the rise of crypto malware mining, ransomware, the workgroup, and what kinds of alternatives exist, BTCManager spoke with Ehrenhofer. Ultimately, as the hacking attempts become more and more sophisticated, a one-size-fits-all approach will no longer suffice.
What should users do in the case that they are infected with Ransomware? There’s a lot of speculation on best practice, but this has been made blurry as of late.
This will vary significantly based on employer policies, but as an individual, I would typically follow these basic steps:
- Look online to see if other users are reporting this same malware, and see if they have been able to evaluate the impact of the attack and identify any weaknesses. In this step, you’re trying to figure out if the attacker just encrypted your computer or something much worse in addition. Perhaps the attacker is a novice and made a mistake that is easy to work around. Unless you possess the technical capabilities of looking through the malware, it’s best to see if any security experts already have. Report it if you can’t find anyone else talking about it.
- I strongly recommend against paying the ransom. This gives attackers a future financial incentive to attack other computers. The attacker could even take your money and run without decrypting your files.
- In the case of ransomware, you should completely reinstall the computer. You will, unfortunately, lose the files in the process, but they are encrypted and inaccessible anyway. You can consider making a copy of the encrypted files on a different hard drive, but don’t connect this hard drive to another computer unless security experts found a workaround and do not know of any malware embedded in these files. Don’t accidentally infect another machine.
- Once you have wiped and reinstalled your computer, restore any backups of files that you have made.
- Set up a backup system so that you can restore files if your computer is infected in the future.
Are the results of the workgroup also applicable to state-wide ransomware attacks? I’m thinking of North Korea’s Lazarus and the general scale of some of these operations.
The workgroup’s resources are currently geared towards people who have no idea what Monero, mining, and ransomware are. They provide useful information for a variety of more technical users, but we do not have anything that currently applies to state-wide ransomware attacks for large organizations. However, if an individual’s computer is compromised by one of the large-scale ransomware operations, our resources may be useful.
Why is it that Monero (and not another privacy coin) is being hijacked to these ends?
Ultimately, attackers like Monero for two reasons: 1) It is private, so they do not need to worry about companies and law enforcement tracing what they do with the Monero after they mine it, and 2) Monero uses a Proof of Work (PoW) algorithm that is CPU and GPU-friendly; thus, the infected machines are competitive. These two components are increasingly distinguishing factors for why attackers choose to mine Monero over other cryptocurrencies.
Unfortunately, Monero is the only major cryptocurrency where every transaction is private. For other cryptocurrencies with privacy features like Dash (DASH), Zcash (ZEC), and Bitcoin (BTC), these privacy features are significantly less supported and used. Especially in the case of ransomware, an attacker will have a much easier time accepting a Monero payment than a fully-shielded Zcash payment.
NEW: The Monero Malware Response workgroup has created a dedicated website to help those who are infected with mining malware, have come across unwanted in-browser mining, or have hit Monero ransomware. Community support for those affected is coming soon!https://t.co/rqFeVFrjU0
— fluffy/pony (@fluffypony) September 25, 2018
How did the Monero community conlcude that a workgroup like this would be helpful?
The initiative was recommended by Riccardo “fluffypony” Spagni as a way of managing some of the recent reports of Monero being used for malicious mining. While we could not prevent malicious mining, we wanted to start by helping those whose machines had been compromised. You can read more about the initial proposal in December 2017 during a community meeting here.
What is the best possible outcome of this? That all Ransomware attacks cease?
We would love for this to be the outcome, but, unfortunately, this is not realistic. This would require every machine to be patched against vulnerabilities, which will likely never happen. Instead, our scope focuses on the victims first to help them if their computers are compromised, and then attempts to spread wider awareness about computer security.
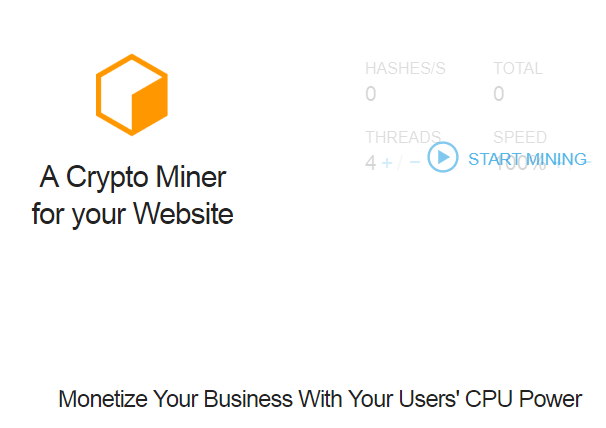
(Source: Coinhive)
Lastly, does the mining-as-substitute-for-advertising narrative really hold promise for small and large media companies?
It depends on the conditions of the network and the nature of the website, but it holds some promise, especially for websites where the user is on the page for a while. I do not expect it to fully replace advertising, but it could function as an additional revenue stream if users are aware of what is happening.
Monero Isn’t Just for Crooks
If the workgroup implies imminent chaos, nothing could be further from the truth. As posited in the final point, a handful of more noble platforms have also “hijacked” the mining software. As mentioned in the original source, similar crypto mining renditions are leveraged by Unicef, Change.org, and BailBloc.
https://twitter.com/Grimezsz/status/938131670011600896
Whether these websites turn a profit at this point is irrelevant; they have already begun to paint a portrait of a Web3 that has corrected for the Internet’s original sin: Banner advertisements. Beyond that, the Monero community is taking a proactive step to negate the cynical features of novel malware. The conversation, if anything, will shed light on an aspect of cryptocurrencies often misunderstood by mainstream media sources.